
We live in the digital age. Information is just a click away and can be accessed across multiple channels such as web, mobile etc. The demand for ubiquitous access to information exposes the organization’s data and systems from multiple endpoints and devices.
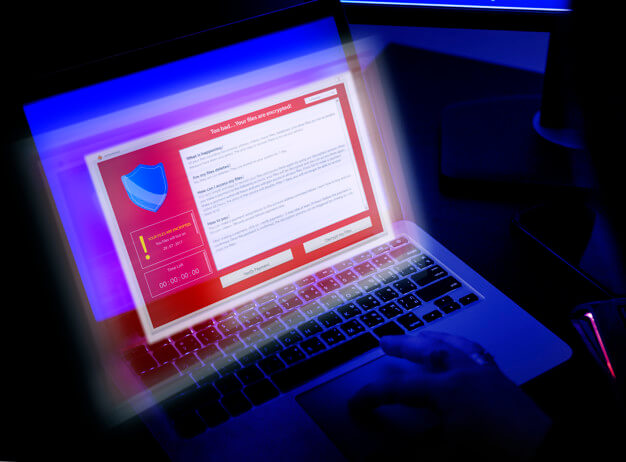
The resultant risk to data, system integrity, identity and privacy presents a huge challenge to organizations today. The need of the hour is to not only prevent and address cybersecurity threats and risks but also to ensure early detection, analysis of attack patterns and prevention and proactive management of cyber-attacks and related risks.
At Clover Infotech, our Centre of Excellence (CoE) has created a comprehensive team of experts in various aspects of cybersecurity such as managing our Security Operations Center (SOC), Database Access Management (DAM), Data Leakage Prevention (DLP), Identity and Access Management (IAM), Endpoint Security etc.
Our Partners:
IBM | Oracle
We have partnered with IBM and Oracle across their Cybersecurity offerings to enable our customers to run their security operations efficiently and mitigate cybersecurity related risks. Our best-in-class SOCs operate from our delivery centers to address the needs of our customers. We have also deployed teams at customer’s sites to ensure comprehensive management of their SOCs, identify patterns and apply analytical models to create pre-emptive and preventive strategies to minimize cybersecurity related threats and risks.
Why businesses need cybersecurity?
Security Operations Center (SOC):
A Security Operations Center (SOC) is a control hub which undertakes the continuous monitoring and assessment of critical applications, websites, databases, servers, networks and assigned devices to check for anomalies and safeguard against any threat or malicious attack.
Our experts come with expertise across the tools in SOC which are called “Security Information and Event Management (SIEM) such as IBM Qradar and IBM Resilient
Database Activity Monitoring (DAM):
Database
activity monitoring (DAM) refers to a suite of tools that can help to monitor,
identify, and alert on fraudulent or unauthorized user activity on a database.
DAM has evolved now to include vulnerability management and classifying issues
as per enterprise applications. It supports security of unstructured data as
well.
Our experts leverage our Database Management expertise to seamlessly manage a variety of DAM tools including Oracle AVDF and IBM Guardium.


Privileged Access Management (PAM):
Privileged Access Management (PAM) is a solution that enables organizations to allow access only to authenticated and validated users. It isolates the use of privileged accounts within the active directory to ensure that these accounts are safeguarded even in a situation where the active directory gets compromised.
At the Clover Infotech Centre of Excellence (CoE), we have built capabilities to work on PAM solutions from Arcos and CyberArk.
Data Loss Prevention (DLP):
Data Loss Prevention (DLP) or Data Leakage Prevention enables organizations to detect data breaches in time and prevents unauthorized and illegal transfer of data outside the organization. Organizations use DLP to protect their personally identifiable information and sensitive data. They also use DLP to adhere to regulatory and compliance mandates and to enable Work From Home and BYOD policies.
Our CoE has built capabilities across solutions from Symantec and Forcepoint for offering DLP services to our customers.


Endpoint Security:
Endpoint security solutions enable organizations to secure the endpoints or devices used by the end users. It comprises laptops, desktops, mobile devices etc. that are used to access enterprise systems and data. Endpoint security software or solutions safeguard the endpoints, which are vulnerable entry points for malicious attack and can be used by cybercriminals to gain unauthorized access into the enterprise’s systems.
Our team of experts are trained on areas across unified endpoint management. We work on solutions such as IBM’s MaaS360, TrendMicro and Symantec.
Vulnerability Management:
Vulnerability Management solutions enable organizations to identify, evaluate, classify, prioritize, remediate, and report vulnerabilities in its systems and the software or applications that run on the systems. Vulnerability Management is a continuous cycle as the organization’s IT footprint is dynamic and slightest of vulnerabilities can create a serious impact.
Our capabilities in Vulnerability Management includes expertise across solutions from Qualys, Nessus etc. among others.

Threat Detection and Response (TDR)
TDR is about utilizing big data analytics to find threats across large and disparate data sets. It is a powerful collection of advanced malware defence tools that identify threat indicators to stop evasive malware attacks. The key benefit is its ability to automatically identify and respond to threats in real time. With TDR, IT teams can set up policies based on threat severity for individuals, devices, and the organization. The automated responses will react to the threats instantly, providing real-time protection, to prevent/minimize the damage to a great extent.

File Integrity Monitoring (FIM)
FIM refers to an IT security process and technology that performs the act of validating the integrity of operating system (OS) and application software files using a verification method between the current file state and a known, good baseline. As opposed to other security measures, FIM solutions are specifically designed to monitor changes in files. The FIM software typically takes a snapshot of your system, and then periodically compares that to the system’s current state.


Reasons to opt for Managed Security Service Provider (MSSP)
1. You are constrained by time, resources, or budget
2. You need to fill a skills gap of your security team
3. You are struggling to hire or retain IT talent with expertise in cybersecurity
4. You have a complex IT infrastructure but it is difficult to get actionable data out of it


Why Clover Infotech?
Document your cybersecurity policies


Benefits of cybersecurity
Cybersecurity solutions provide digital protection to your business, It will ensure that your employees aren’t at risk from potential threats such as Adware and Ransomware.
Viruses can slow down computers to a crawl and make work practically impossible. Effective cybersecurity eliminates this possibility, maximizing your business’ potential output.
By ensuring that your business is secure from cyber threats, it will also protect your customers, who could be susceptible to a cyber-breach by proxy.
Educate all employees


Why businesses need cybersecurity?
Regularly back up all data


Install anti-malware software
Use multifactor identification


• Detect
• Anomalies and Events
• Security Continuous
• Monitoring
• Detection Processes

• Respond
• Response Planning
• Communications
• Analysis
• Mitigation
• Improvements

• Recover
• Recovery Planning
• Improvements
• Communications


